VBO365: Use pre-created Azure AD application for authentication
Referring to the previous article on creating Azure AD applications with my script, I today want to describe how to add an organization to VBO with this pre-created certificate.
Prerequesites
To start off with this you’ll need the following data:
- Veeam Backup for Microsoft Office 365 installed with at least one repository configured
- The Azure AD application ID, either from the Azure AD portal or from the output of my script
- The key-file (PFX) to authenticate against this application and the password to decrypt the key-file
- An Exchange Admin user you want to use for impersonation for Exchange backups (only if you want to protect Exchange or Teams)
You only need the user account name, but you won’t need to have full credentials for this user in this phase.
I used my script to create the certificate and will refer to it. I’ve used the following command and got the following registration details out of it:
PS> .\vbo-create-azure-ad-app.ps1 -azureTenantId 0ea4ffc9-e625-43a1-a751-82c7e35a9fba -appName VBO_BACKUP_ONLY -limitUsageTo Backup -certificateFilePath .\vbo_backup_only.crt -keyFilePath .\vbo_backup_only.pfx -keyLifeTimeDays 90 ... App-ID: 21989c42-3bfe-4e95-b5da-32d382eb7477 App-Name: VBO_BACKUP_ONLY Key-File: .\vbo_backup_only.pfx ...
Add your organization
The basic process of adding a modern app-only organization is already perfectly described in the Veeam Help Center, so I will go only briefly over the default settings and in more detail where we do changes.
I start by adding an organization and keep the defaults on the first two pages of the wizard (O365 connection settings).
This will get me an Office 365 org, with all services enabled for backup and modern-app only authentication in the default region.
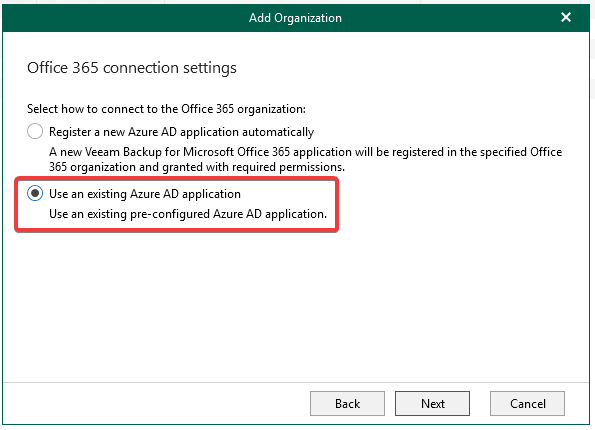
On the third wizard page I choose to “Use an existing Azure AD application”:
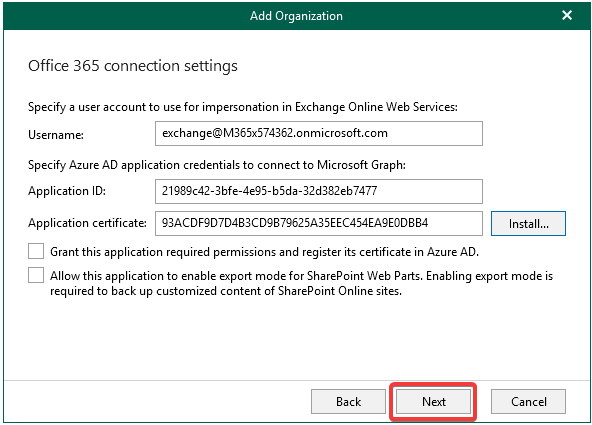
On the next page enter your Exchange admin user to be used for impersonation. You won’t need any credentials for this user, but just specify the username.
From the script (or Azure AD portal) you can now use the application ID. It’s important to then uncheck the box for granting the application the required permissions – we’ve added these permissions beforehand, so we don’t need this here.
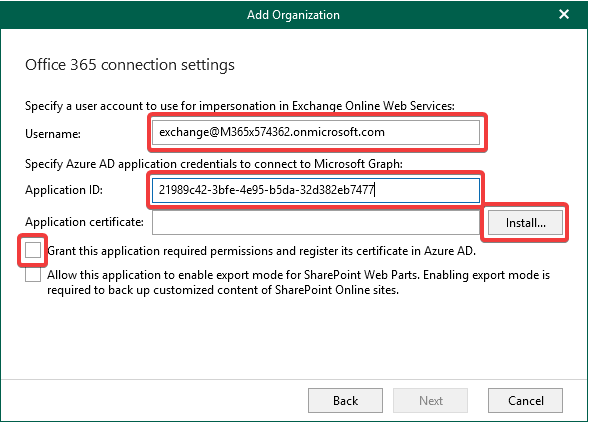
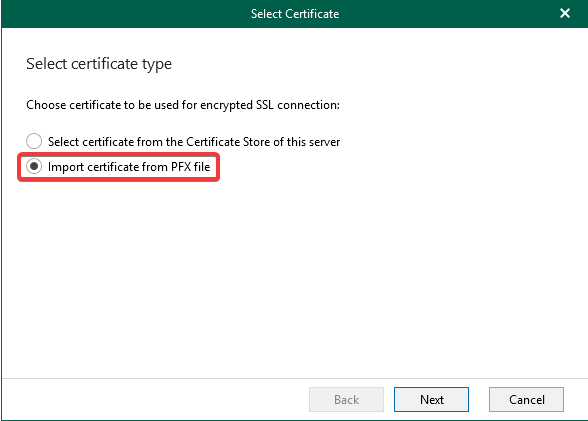
Finally on this page click on the “Install…” next to the Application certificate and select to import a certificate from a PFX file:
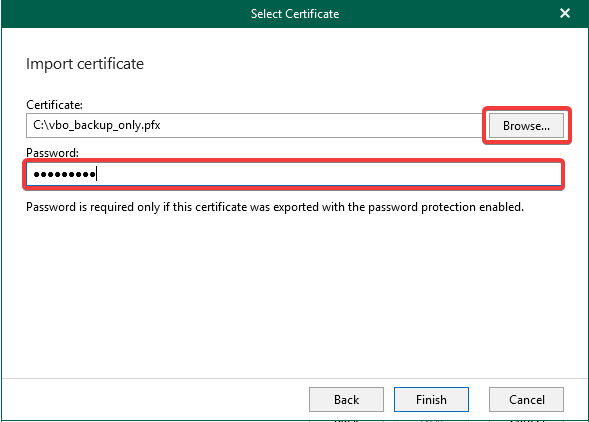
On the next page browse to the PFX certificate that you’ve copied to your VBO machine previously and give the passphrase to access the key.
After clicking Finish you’ll see a hash identifying the application certificate in the wizard and can click Next on this page:
In the final stage you should get all green check marks for the verification. If you get access denied at this point please check with your Azure global admin if the permissions were granted on the app as requested by the script.
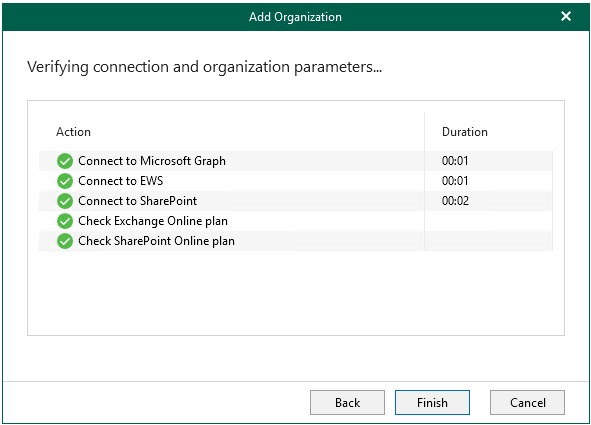
After finishing the wizard off you have your organization set up and can start creating backup jobs for all the services by leveraging the previously created application.
One Reply to “VBO365: Use pre-created Azure AD application for authentication”